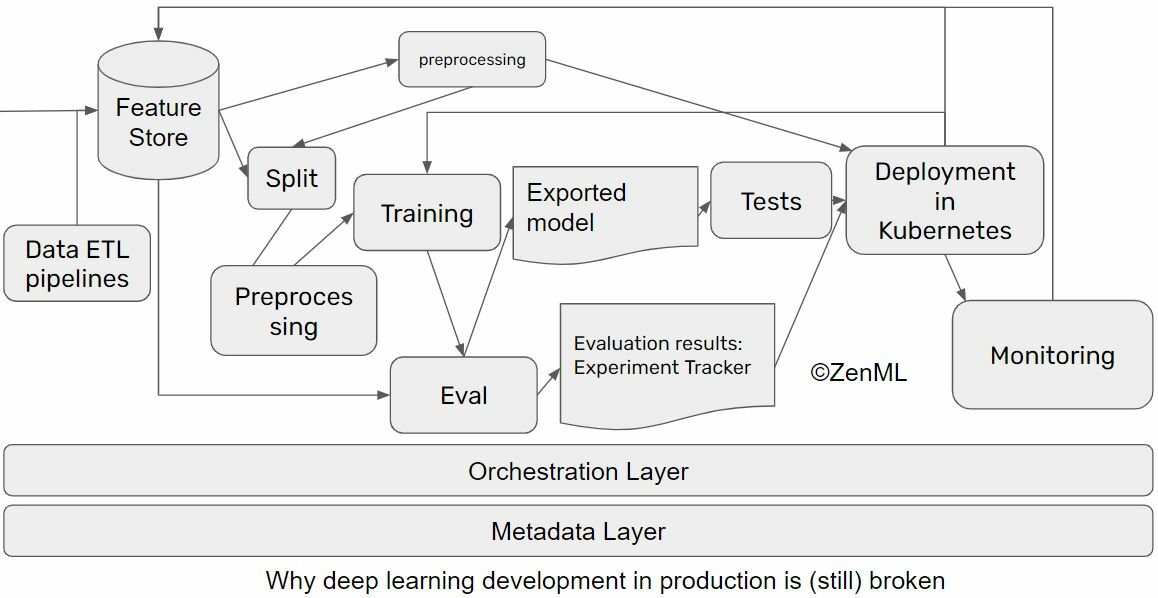
Why ML in production is (still) broken and ways we can fix it
Hamza Tahir on HackerNoon:
By now, chances are you’ve read the famous paper about hidden technical debt by Sculley et al. from 2015. As a field, we have accepted that the actual share of Machine Learning is only a fraction of the work going into successful ML projects. The resulting complexity, especially in the transition to “live” environments, lead to large amounts of failed ML projects never reaching production.
Productionizing ML workflows has been a trending topic on Practical AI lately…