The Cryptography Research Group at Microsoft released Microsoft SEAL to encrypt and secure sensitive data in the cloud
If you’ve been watching the news, you know that the latest data breach involved Marriott exposing 500 million guest reservations from its Starwood database. The kicker is that the unauthorized access to the Starwood guest database stretches back to 2014. That’s FOUR YEARS of unfettered access to this database!
It’s breaches like these that helped motivate the team at the Cryptography Research Group at Microsoft to be “extremely excited” to announce the release of Microsoft SEAL (Simple Encrypted Arithmetic Library) as open source under the MIT License.
The heart of this new library is powered by Homomorphic Encryption, which is now ready to be standardized. Homomorphic Encryption (HE) allows computations to be done on encrypted data, without requiring access to a secret (decryption) key. The data can be stored encrypted in the cloud without the need to download it to perform any useful operations.
This release couldn’t have been timed any better. “This is the right moment to put this library in the hands of every developer, so we can work together for more secure, private, and trustworthy computing,” says Kristin Lauter, Principal Researcher and Research Manager for the Cryptography group at Microsoft Research.
This pull-quote from the announcement post summarizes the need for Microsoft SEAL quite well:
As we increasingly move our data to the cloud, there is a clear concern that arises: How can we balance convenience and privacy? … we share personal information with service providers because we have few other options. With traditional encryption schemes, it is impossible to run any computation on encrypted data. So either we store our data encrypted in the cloud and download it to perform any useful operations, which can be logistically inconvenient, or we provide the decryption key to service providers, risking our privacy. Until now.
A refresher on recent data breaches
In the last several years we’ve seen several large scale data breaches happen. Here are just a few to remind folks how exposed we really are “in the cloud.”
- Yahoo confirmed in September 2016 that all 3 Billion user accounts were impacted by their 2013 security breach
- eBay had 145 Million users compromised in May 2014 and confirmed the breach exposed names, addresses, dates of birth and encrypted passwords. The hackers had complete inside access for 229 days thanks to the credentials of three corporate employees.
- Equifax had a breach on July 29, 2017 which impacted the personal information (including Social Security Numbers, birth dates, addresses, and in some cases drivers’ license numbers) of 143 Million consumers. 209,000 of those consumers also had their credit card data exposed.
- Target Stores confirmed in December 2013 that credit/debit card information and/or contact information of up to 110 Million of its customers was compromised. The estimated cost of the breach was $162 Million.
While watching a recent YouTube video from my buddy Tom Lawrence, of Lawrence Technology Services, he said his “faith is waining in the U.S. Justice system to actually set forth any punishment on these companies because because we generally see these data breaches and it goes back to business as usual.” Tom goes on to ask this poignant question, “Have any of these companies actually gone out of business because of one of these data breaches?”
Honestly, I don’t know the answer to that very good question. If you do, let us know.
Request for comments
We reached out with a request for comments to Kristin Lauter, Principal Researcher and Research Manager for the Cryptography group at Microsoft Research. Here are the questions we asked and the responses she and the team provided about Microsoft SEAL.
How would Microsoft SEAL be useful in the case of a data breach?
If Microsoft SEAL is used to encrypt sensitive data, then if there is a data breach, the confidentiality of the data is still protected. The thief would need to have the secret key in order to get any useful information from the SEAL-encrypted data.
Could you share a common use of Microsoft SEAL?
A classic use case is: a company wants to store sensitive data about their business operations on the Microsoft cloud. They use Microsoft SEAL to encrypt the data and keep the key to themselves. Once the data is uploaded to the cloud, the company can ask for data analytics or Machine Learning or AI predictions to be computed on the encrypted data, and the cloud vendor can return the results of the computation, using SEAL, without ever decrypting the data. The company decrypts the results locally. This system allows long-term storage and asynchronous access to the data over time, offering the convenience of cloud storage and computation, combined with the security and confidentiality provided by SEAL Homomorphic Encryption.
Why is it important for Microsoft SEAL to be “free of external dependencies”?
Often Crypto libraries require complicated math, and some implementations use third party libraries to implement the mathematical functions, such as large polynomial arithmetic, modular arithmetic, etc. However, this can create all kinds of challenges, such as license issues, complexity in deploying on unusual platforms, and increased complexity for support. Because SEAL has no such dependencies it is easy to use in almost any environment, such as on IoT devices which often collect highly private data. Since our team has developed every part of SEAL, we can very efficiently address possible problems and improve the library quickly when necessary.
If you have questions for the team behind this project, start a discussion below. They’re listening.
Invite to discuss and participate in open source
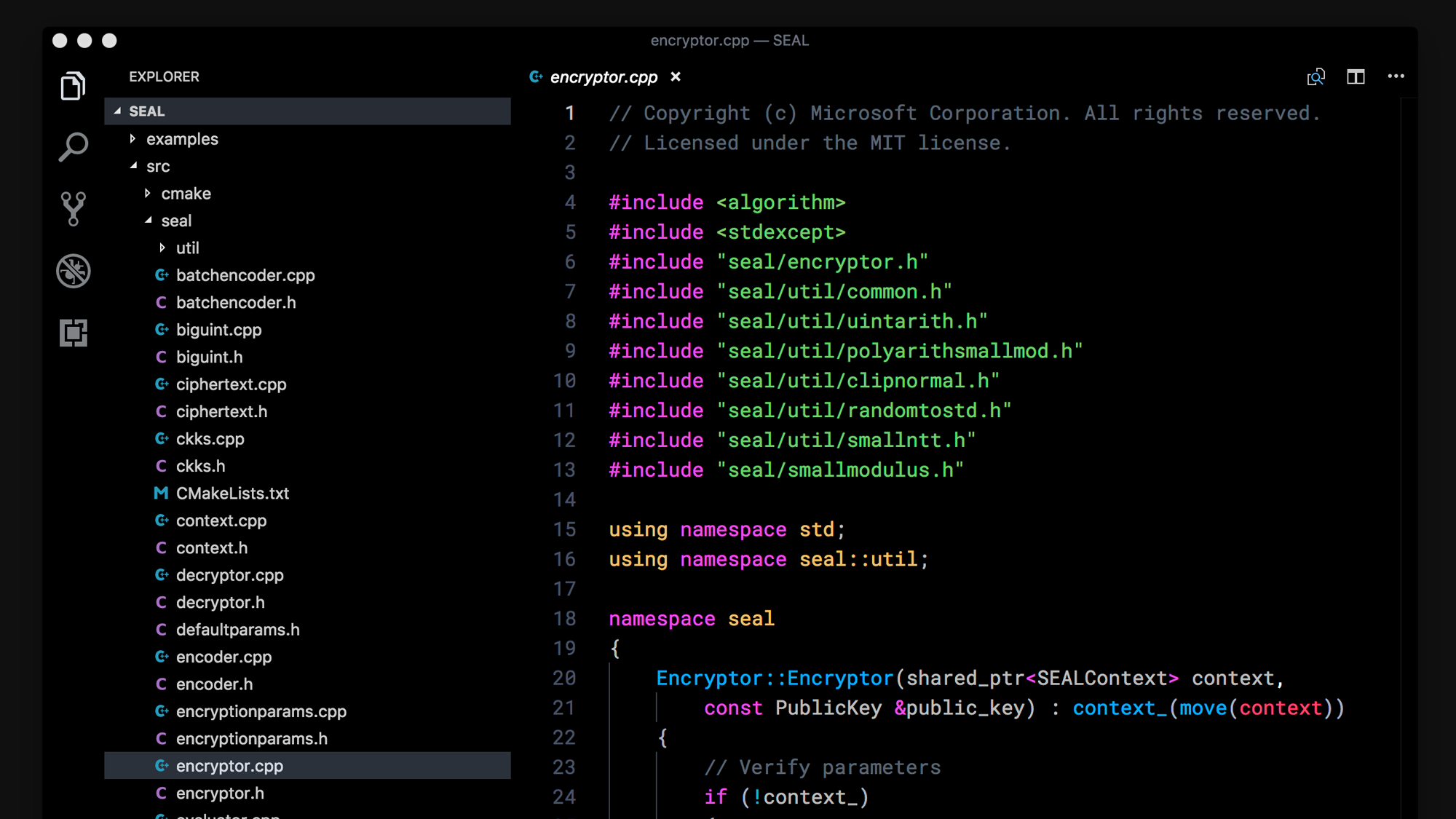
The team behind this project are looking for ways to engage with the open source community to continue developing this library. Microsoft SEAL is written in standard C++ which makes it easy to compile in many different environments.
They have extended a “warm invite” to check out the GitHub repo.
Be sure to listen and subscribe to Practical AI too. We’re working on a full-length podcast covering this project featuring Kristin Lauter, Kim Laine, and Sreekanth Kannepalli.
Discussion
Sign in or Join to comment or subscribe